third Party Risk Management
,
Application Security
,
Blockchain & Cryptocurrency
From Ransomware to Log4j, a Compilation of Stories, Podcasts and Expert Analysis
This previous 12 months has been a whirlwind for cybersecurity leaders. From watching the developments of late 2020’s unprecedented SolarWinds cyberattack unfold within the New Year to ending with the Log4j vulnerability saga, 2021 has been one other document 12 months for info safety – and the velocity of information developments won’t abate any time quickly.
See Also: OnDemand Webinar | MSPs: Review 2021 Cybercrime Tactics, Prepare Your 2022 Cyber Defenses
Here is a compilation of some of 2021’s must-read tales – categorized by breaking information occasions, ransomware evaluation, greatest video interviews and cybersecurity predictions for 2022.
Global Breaking News Events
Information safety information made many headlines this 12 months, crossing into most mainstream information retailers.
In the United States, the Biden administration responded to the rise in ransomware assaults – together with Kaseya, Colonial Pipeline and different assaults on vital infrastructure – exhibiting a rising authorities concentrate on safety protection within the United States. The U.S. and the world are additionally grappling with how cryptocurrency will play into the long run of finance. How will these new legal guidelines and laws within the cyber sphere have an effect on the safety business within the New Year?
From a world perspective, there have been many different main occasions that affected the safety world: the Conti ransomware assault on Ireland’s healthcare system, India’s authorities rollout of the Citizen Financial Cyber Fraud Reporting and Management System and the U.Ok. grappling with knowledge privateness and safety legal guidelines, amongst different security-related occasions.
Is there a serious information occasion that ISMG lined in your area that has not made this checklist? Share it with us on social media via Twitter (@ISMG_News) or LinkedIn (Information Security Media Group – ISMG).
Severe Apache Log4j Vulnerability Threatens Enterprise Apps
A zero-day vulnerability detected within the Java logging library Apache Log4j can lead to full server takeover and leaves numerous functions weak, in response to safety researchers, who say that the simply exploitable flaw was first detected within the common sport Minecraft. Experts are predicting the consequences of Log4j might have an effect on the safety business for years to come back (see: Log4j Updates: Flaw Challenges Global Security Leaders).
Colonial Pipeline Ransomware Attack
In May, the Colonial Pipeline ransomware assault struck – inflicting the corporate to close down greater than 5,000 miles of pipeline for every week – and formed the way in which safety leaders mentioned this matter for the remainder of the 12 months. The Biden administration revealed early on that the assault had been carried out via the DarkSide pressure of ransomware and prompted Congress to place ransomware laws entrance and middle. Colonial Pipeline CEO Joseph Blount was severely criticized for his dealing with of the assault, and Congress questioned what he might have carried out higher to deal with the nation’s vital pipeline networks.
Kaseya Ransomware Attack: ‘Largest Attack I’ve Witnessed’
Like Colonial Pipeline and SolarWinds, the Kaseya cyberattack, which occurred in July, was a serious shifting level in how safety practitioners considered safety greatest practices, in addition to preparation and mitigation methods. Mark Loman of Sophos went on the document to say Kaseya was the most important assault he had witnessed and predicted that 1000’s of organizations worldwide could be affected by the incident. Victims of the Kaseya assault have been later victimized in separate malware campaigns.
Video: SolarWinds Supply Chain Hack: Investigation Update
SolarWinds was reported in December 2020 and new developments about this main cyberattack lasted effectively into 2021. In January 2021, the ISMG Security Report described new particulars rising from the SolarWinds provide chain hack investigation (see: Severe SolarWinds Hacking: 250 Organizations Hit?).
India Launches Effort to Track, Freeze Cyber Fraud Proceeds
The Indian authorities arrange, in June, the Citizen Financial Cyber Fraud Reporting and Management System to report, observe – and in the end freeze – the proceeds of cyberattack-induced monetary theft.
US to Unveil Sanctions on Use of Cryptocurrency for Ransoms
As early as this week, the Biden administration might unveil plans to curtail the ransomware assaults which have crippled company networks this 12 months. According to a report from The Wall Street Journal, the Treasury Department will announce sanctions and comparable steering designed to disrupt the monetary infrastructure that has enabled ransomware assaults thus far.
Regulators: Banks Have 36 Hours to Report Cyber Incidents
U.S. federal banking regulators have authorized a brand new rule that can require banks to inform regulators no later than 36 hours after the group determines it has suffered a qualifying “computer-security incident,” the nation’s high monetary companies introduced in November.
UK Looks to Revamp Data Privacy Policies Post-Brexit
The U.Ok. is making ready to revamp the nation’s knowledge safety and privateness legal guidelines as a method to spur financial progress and innovation in its post-Brexit financial system, in response to the Department for Digital, Culture, Media and Sport.
T-Mobile Probes Attack, Confirms Systems Were Breached
T-Mobile USA confirmed that its laptop programs have been illegally accessed, following experiences of an obvious intrusion. But the Bellevue, Washington-based cellular communications subsidiary of Germany’s Deutsche Telekom says it is nonetheless investigating whether or not prospects’ private buyer knowledge was uncovered.
Deepfakes, Voice Impersonations Used in Vishing-as-a-Service
While organizations are grappling with methods to sort out what some researchers says is a 35% spike in e mail phishing assaults, cybercriminals have upped the ante to maneuver to extra refined methods – utilizing superior deepfake and voice impersonation applied sciences to bypass voice authorization mechanisms and for voice phishing, or vishing, assaults.
Cryptocurrency Exchange Bug Reveals ‘WannaCry 2.0’ Clues
In this ISMG Security Report, Jeremy Kirk discusses how flaws within the programs of ShapeShift, a U.Ok.-based cryptocurrency change, reveal how a North Korean-linked group laundered cryptocurrency that got here from a infamous ransomware assault in 2017.
Apple’s Image Abuse Scanning Worries Privacy Experts
Apple unveiled a brand new system for detecting youngster sexual abuse images on its gadgets, however laptop safety consultants concern the system might morph right into a privacy-busting software. The system, referred to as CSAM Detection, is designed to catch offensive materials that is uploaded to iCloud accounts from gadgets. It works partially on a tool itself – a element that privateness and safety consultants say might open a door to broader monitoring of gadgets.
Missouri Refers Coordinated Bug Disclosure to Prosecutors
A newspaper reporter in Missouri who responsibly reported the publicity of Social Security numbers on a state authorities web site has been accused of malicious hacking by the state’s governor.
Ransomware Attacks – Analysis and Breakdown

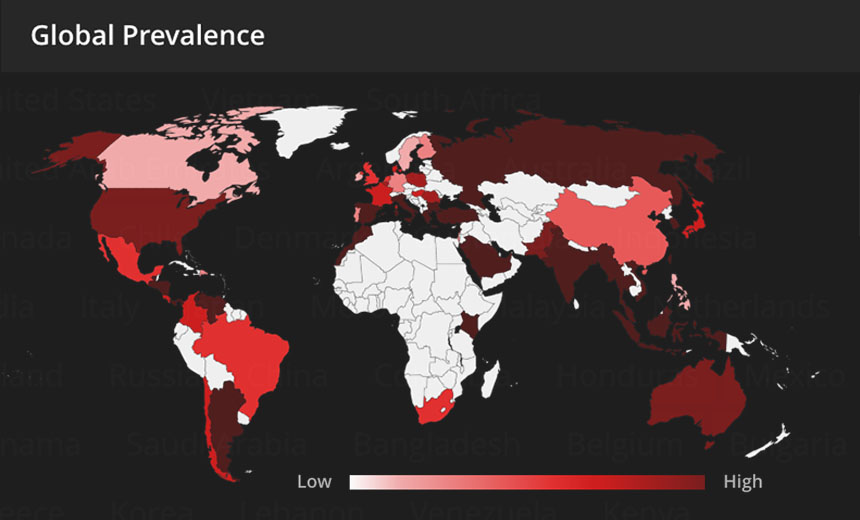
Ransomware continues to be a high menace globally, with consultants predicting how menace actors’ methods and cyber insurance coverage insurance policies will evolve. Nation-states and legal teams haven’t slowed down on launching campaigns devoted to espionage, ransomware as a service, and normal disruption focusing on vital infrastructure around the globe.
The Ransomware Files
In an effort to offer extra depth to ransomware protection, Jeremy Kirk launched the brand new podcast miniseries “The Ransomware Files,” which provides listeners the possibility to expertise what it’s like being within the trenches as a ransomware assault unfolds.
Each episode includes a visitor discussing what it’s like being the sufferer of ransomware – detecting the menace, deciding whether or not to pay the ransom, and sharing what was realized to offer further protection ways for IT safety groups. All episodes are at the moment accessible to obtain in your most popular podcast streaming platform.
The Ransomware Files, Episode 1: The School District
The Ransomware Files, Episode 2: Bridging Backup Gaps
The Ransomware Files, Episode 3: Critical Infrastructure
FBI DarkSide Ransomware Used in Colonial Pipeline Attack
The FBI and the White House confirmed that the DarkSide ransomware variant was used within the Friday assault that prompted disruptions at Colonial Pipeline Co., which operates a 5,500-mile pipeline that provides gasoline, gasoline and different petroleum merchandise all through massive parts of the japanese U.S.
Biden Orders Investigation of Kaseya Ransomware Attack
U.S. President Joe Biden has ordered federal intelligence companies to research the incident involving IT administration software program vendor Kaseya, which sustained a suspected REvil ransomware assault. Attackers reportedly compromised Kaseya’s distant monitoring system, VSA, forcing the corporate to induce its managed service supplier prospects to quickly shut down their on-premises servers for at the very least the subsequent 24 to 48 hours.
Ransomware Disrupts Scottish Environment Protection Agency
The Scottish Environment Protection Agency says a ransomware assault final month continues to trigger severe outages and warns that ransom-demanding attackers additionally stole some knowledge.
Meat Processing Grinds to Halt After ‘Cybersecurity Attack’
The world’s largest meat provider, JBS, says an “organized cybersecurity attack” has led it to close down servers in North America and Australia, and consultants say a chronic outage might have a noticeable affect on the worldwide provide of meat.
Ryuk Ransomware Profits: $150 Million
Researchers say cryptocurrency wallets utilized by the operators behind the Ryuk ransomware pressure and the gang’s associates maintain greater than $150 million.
Ransomware Landscape: REvil Is One of Many Operators
For cracking down on particular person ransomware operations, one hurdle stays on the present menace panorama: As ever, a number of strains of crypto-locking malware are being utilized by many various attackers – not simply operations and associates primarily based in Russia – and there is a fixed inflow of new strains and gamers, pushed by the rising income to be obtained by way of ransomware, and backed by a vibrant cybercrime-as-a-service financial system.
Ransomware: Beware of 13 Tactics, Tools and Procedures
Defenders throughout each sort of focused group – together with authorities companies and personal companies – would do effectively to have simpler defenses in place. Such defenses would ideally embrace organizations proactively in search of identified ransomware attackers’ ways, methods and procedures. That variety of menace searching might help defenders spot assaults within the reconnaissance part earlier than they progress to knowledge being exfiltrated or programs getting crypto-locked.
Alert for Ransomware Attack Victims: Here’s How to Respond
As ransomware continues to pummel organizations, in the event that they do get hit, then from an incident response standpoint, what are the important first steps they need to take to clean their restoration?
Secrets and Lies: The Games Ransomware Attackers Play
If you are a legal, practising good operational safety would appear to preclude granting tell-all information media interviews. And but we have seen a spate of attackers who wield ransomware – together with MountLocker, LockBit, REvil and DarkMatter – sharing insights into their inclinations, motivations and ways.
Ransomware Attack Leads to IT Shutdown for Irish Hospitals
After Health Service Executive, Ireland’s state well being providers supplier, shut down all its IT programs serving hospitals within the wake of a ransomware assault in May, some safety consultants praised its decisive motion and refusal to pay a ransom.
Lawsuit: Hospital’s Ransomware Attack Led to Baby’s Death
The medical malpractice lawsuit – connecting the loss of life of an toddler to a 2019 ransomware assault – is doubtlessly the primary within the U.S. alleging a loss of life tied to a hospital ransomware assault, is a stark instance of what some consultants have been fearfully warning about in latest months.
Australia Plans Ransomware Attack Reporting Requirement
Australia plans to require bigger companies to report ransomware assaults to the federal government, as half of a complete technique that additionally contains new legal penalties and help for victims.
Why Ransomware Is a Game Changer for Cyber Insurance
Ransomware assaults have turn out to be the sport changer in driving up safety necessities, coverage premiums and rejection charges for healthcare sector entities searching for new cyber insurance coverage insurance policies or renewals, says Doug Howard, CEO of privateness and safety consultancy Pondurance.
ISMG’s Video Interviews With InfoSec Thought Leaders
If you missed watching any of these video interviews, listed below are a couple of must-watch discussions ISMG’s editorial workers rounded up. From “passwordless” expertise to zero belief, these interviews with main business professionals can provide perception on developments that can absolutely proceed to develop in 2022.
The Best of RSA Virtual Conference 2021
RSA got here from the digital stage in 2021, and resilience was the becoming theme for the 12 months. ISMG changed its ordinary two dwell on-site studios with a set of residence studios and produced a various group of interviews on well timed subjects with thought leaders who will probably be fixing cybersecurity’s most pressing issues. ISMG performed greater than 100 interviews with the world’s main safety consultants.
Jim Clark: Why He’s Giving Away Passwordless Technology
When he co-founded the agency Beyond Identity in 2020, serial entrepreneur Jim Clark stated he felt considerably liable for the proliferation of passwords. Now he and accomplice Tom Jermoluk are doing one thing about it. They are offering entry to their passwordless expertise at no cost.
Equifax CISO Jamil Farshchi on SolarWinds and Supply Chains
Jamil Farshchi has been there. As CISO of Equifax, he is aware of what it’s prefer to be a sufferer of a high-profile cyberattack. And he is aware of breached corporations have a alternative: “Are they going to be a force for good by helping the rest of the industry learn from their experience?”
Unscripted: 3 Security Leaders Dissect Today’s Top Trends
No script, no filter: Just Microsoft’s Edna Conway and Cisco’s Wendy Nather gathering with privateness chief Michelle Dennedy to debate the affect of the SolarWinds provide chain assault and to play Buzzword Mystery Date with safe entry service edge, buyer identification and entry administration, and “passwordless” authentication. Are these cybersecurity developments dreamboats or duds?
World Health Organization CISO on Supply Chain Risk
Flavio Aggio, CISO of the World Health Organization, has had a protracted profession throughout many sectors. He understands provide chain threat, and he sees the SolarWinds hack as “resumption of a very old attack – in new packaging.” He presents insights on mitigating this and different cybersecurity dangers.
‘Zero Trust’: An Outdated Model?
The zero belief mannequin is outdated in in the present day’s cloud setting, says Ian Thornton-Trump, CISO at Cyjax, a menace intelligence firm, who recommends the use of segmentation and monitoring for anomalous conduct as an alternative.
Colonial Pipeline: ‘A Global Day of Reckoning’
Gregory Touhill, the retired Air Force normal and former federal CISO underneath President Obama, minces no phrases when he describes the Colonial Pipeline ransomware assault as a “global day of reckoning” for vital infrastructure safety.
SolarWinds, Ransomware and the State of the Industry
Over the previous 12 months, we have seen improvement for the SolarWinds assault, the Microsoft Exchange Server exploits and the Colonial Pipeline ransomware strike. The threats are extra imminent than ever. But Philip Reitinger of the Global Cyber Alliance believes strongly: We created this mess, and we will repair it.
Art Coviello: ‘It’s a Roaring ’20s for Technology’
From identification and entry administration to cloud migration and related gadgets, retired RSA CEO Art Coviello appears past the pandemic and says, “It’s going to be a Roaring ’20s for technology.” But he additionally foresees a doubtlessly calamitous decade for safety.
CISO Spotlight: Marene Allison, Johnson & Johnson
As CISO of Johnson & Johnson, Marene Allison was used to gauging her safety posture by the highest menace exercise: nation-state, cybercrime, insider or hacktivist. But in 2020, all of them struck directly. Here is one CISO’s tackle the state of the business.
China’s Cyberattacks: Sizing Up International Response
The U.S and its allies formally accusing China of cyberattacks on Microsoft Exchange servers comes as no shock as a result of it is “indicative of the behavior of the administration in China for many years now,” says Cybereason CSO Sam Curry.
ISACA 2021 Report: Top Trends, Improving Cyber Maturity
Key challenges from the latest State of Cybersecurity 2021 embrace, “Integrating risk with maturity and keeping up with industry trends,” says Jenai Marinkovic, member of the ISACA Emerging Trends Working Group.
Using Psychology to Increase Organizational Resiliency
Including psychology in cybersecurity instructional consciousness applications permits workers to acknowledge and belief their very own instincts when coping with a possible safety incident, says Denise Beardon, head of info safety engagement Ransomware continues to be a high menace with consultants predicting how menace actors’ methods and cyber insurance coverage insurance policies will evolve.
2022 Predictions in Cybersecurity – Analysis and Trends
As we wrap up 2021, many are doubtless pondering: What subjects and developments would be the most crucial for safety groups in 2022? Check out the most recent movies and articles – that includes main safety consultants and professionals – for discussions about what’s on the horizon.
Cyber Attacks: The 2022 Predictions
On the heels of provide chain assaults, vital infrastructure hits and ransomware gone wild, what extra can we count on from cyber attackers in 2022? Plenty, says Derek Manky of Fortinet’s FortiGuard Labs. He particulars his New Year predictions.
COVID-19: How Does Omicron Change the Discussion?
As of Dec. 13, 2021, the UK is going through a “tidal wave” of infections from the COVID-19 Omicron variant, and case numbers are rising in North America as effectively. What do well being consultants know to date in regards to the unfold and severity of Omicron infections? Pandemic knowledgeable Regina Phelps shares insights.
Zero Trust: John Kindervag’s 2022 Outlook and Predictions
On the cusp of 2022, John Kindervag – the daddy of the Zero Trust safety mannequin – displays on how the Zero Trust dialogue has advanced in 2021 and makes his New Year’s predictions. Will the president’s government order be an accelerator or an anchor? Which myths are ripe to be busted?
Forrester Predictions: Rethinking Supply Chain Management
Principal analysts at Forrester, Sandy Carielli and Jeff Pollard, focus on their newest analysis, Predictions 2022: Cybersecurity, Risk and Privacy, which highlights the necessity for gaps in third-party relationships, collaboration and belief to be addressed.
Synthetic ID Fraud: What to Look Forward to in 2022
Automation, an excellent legal community and the power to make use of accounts as an alias are some of the components contributing to artificial ID fraud, says a panel of three consultants – Karen Boyer, vice chairman, fraud at People’s United Bank; John Buzzard, lead fraud and safety analyst at Javelin Strategy and Research; and Greg Woolf, CEO of FiVerity.
The Need to Think Differently About Cybersecurity in 2022
As ransomware assaults proceed to pose a major menace to enterprises and people, “We will keep banging the message that basic cyber hygiene makes a big difference to lots of people,” says Andy Bates of the Global Cyber Alliance.
Ransomware and the C-Suite: What Do Executives Want to Know?
What does the C-suite need to learn about its group’s ransomware preparedness and response methods? Clar Rosso of (ISC)² shares findings from the corporate’s new report that gives insights into the minds of C-suite executives and the way they understand their organizations’ readiness for ransomware assaults.
NATO’s NCI Academy: Training Tomorrow’s Cyber Leaders
Garry Hargreaves, director of the NATO Communications and Information – or NCI – Academy, says the academy goals to organize “the leaders of tomorrow” for a “volatile world.”
Cryptocurrency Compliance Cooperative: The Road Map for 2022
The cryptocurrency business has come collectively and shaped a gaggle referred to as the Cryptocurrency Compliance Cooperative. What is the goal of this group, and the way will it assist the business? Three consultants – Ari Redbord, head of authorized and authorities affairs, TRM Labs; Seth Sattler, Bank Secrecy Act officer, Digital Mint; and Michael Fasanello, director of coaching and regulatory affairs on the Blockchain Intelligence Group – share their insights.
Why Healthcare Will Remain a Top Cyberattack Target in 2022
Two years into the pandemic, pharmaceutical corporations stay a high goal for cybercriminals, and that development will undoubtedly persist, says former Department of Defense menace analyst Paul Prudhomme.


